GitOps - CD for cloud native apps

tldr;
- GitOps is a pull based model that uses Git as the source of truth for application and Infra code. State (Actual vs Desired) is managed via an operator that runs in your kubernetes cluster
What is it
GitOps is a paradigm for kubernetes cluster management that uses Git as the source of trust for declarative applications and infrastructure
How is it different
GitOps is a pull-based model
-
The majority of CI/CD tools available today use a push-based model. A push-based pipeline means that code starts with the CI system and then continues its path through a series of encoded scripts to push changes to the Kubernetes cluster
-
Pull relates to the Operator installed to the cluster that watches the image repository for new updates
Why use this approach
- GitOps takes full advantage of the move towards immutable infrastructure and declarative container orchestration
- The approach helps to prevent configuration drift
What does this look like
In a pull pipeline, a Kubernetes Operator reads new images from the image repository from inside of the cluster.
At the centre of the GitOps pattern is the Operator/Agent. It monitors the single source of truth (a config repo) that contains deployment manifest and the actual state in the cluster
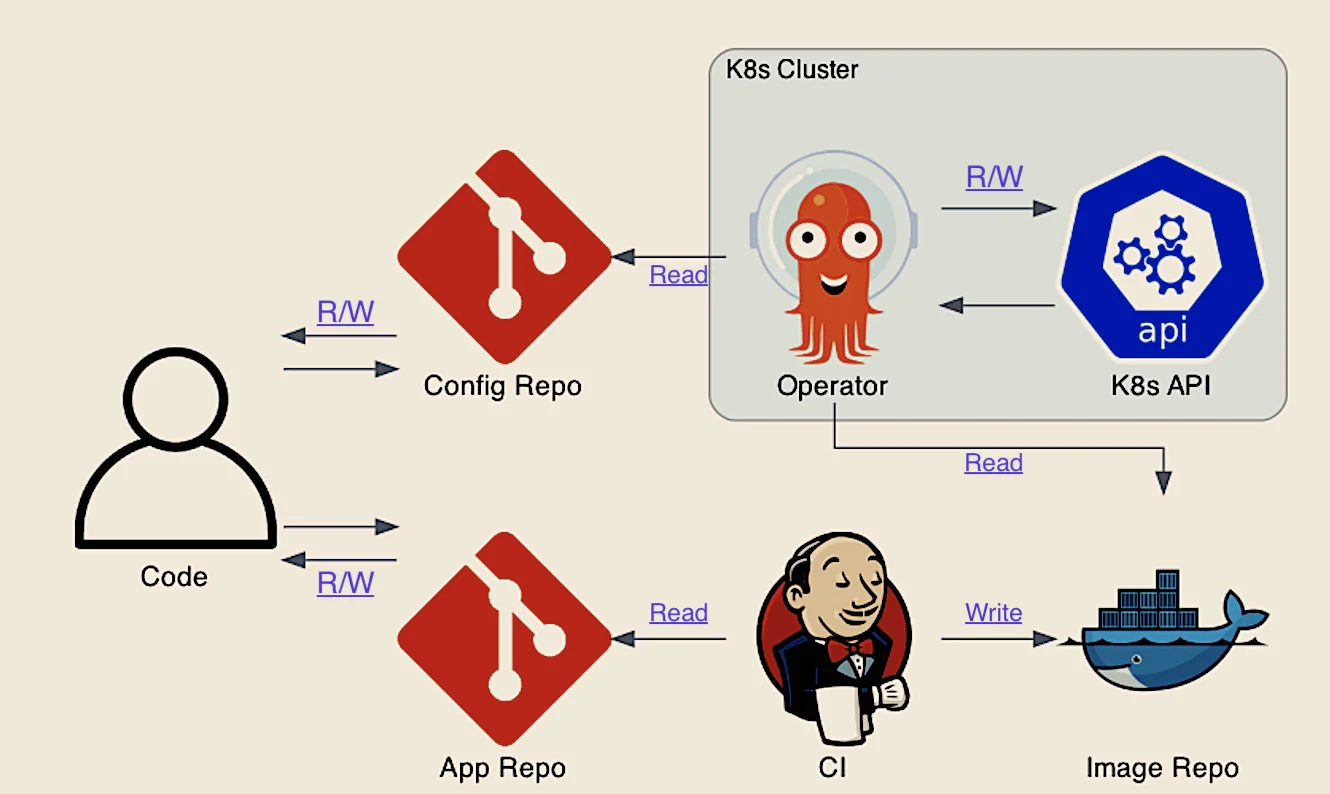 The Operator constantly monitors the Actual State in the cluster, and the Desired State defined in the Repo
The Operator constantly monitors the Actual State in the cluster, and the Desired State defined in the Repo
Separation of concerns
The pipelines can only communicate by Git updates:
- Whenever Git is updated, the Operator is notified.
- Whenever the Operator detects drifts, monitoring and alerting tooling are notified
Benefits
- Consistency
- -> Prod states matches your test env’s
- Reliability
- -> With Git’s capability to revert/rollback and fork, you gain stable and reproducible rollbacks
- Developer Experience
- -> Focus on dev code rather than kubernetes exp (faster onboarding)
- Standards and Consistency
- -> One model for apps, Infra and kubernetes changes
- Enhanced security
- -> reduced potential to expose credentials outside of your cluster
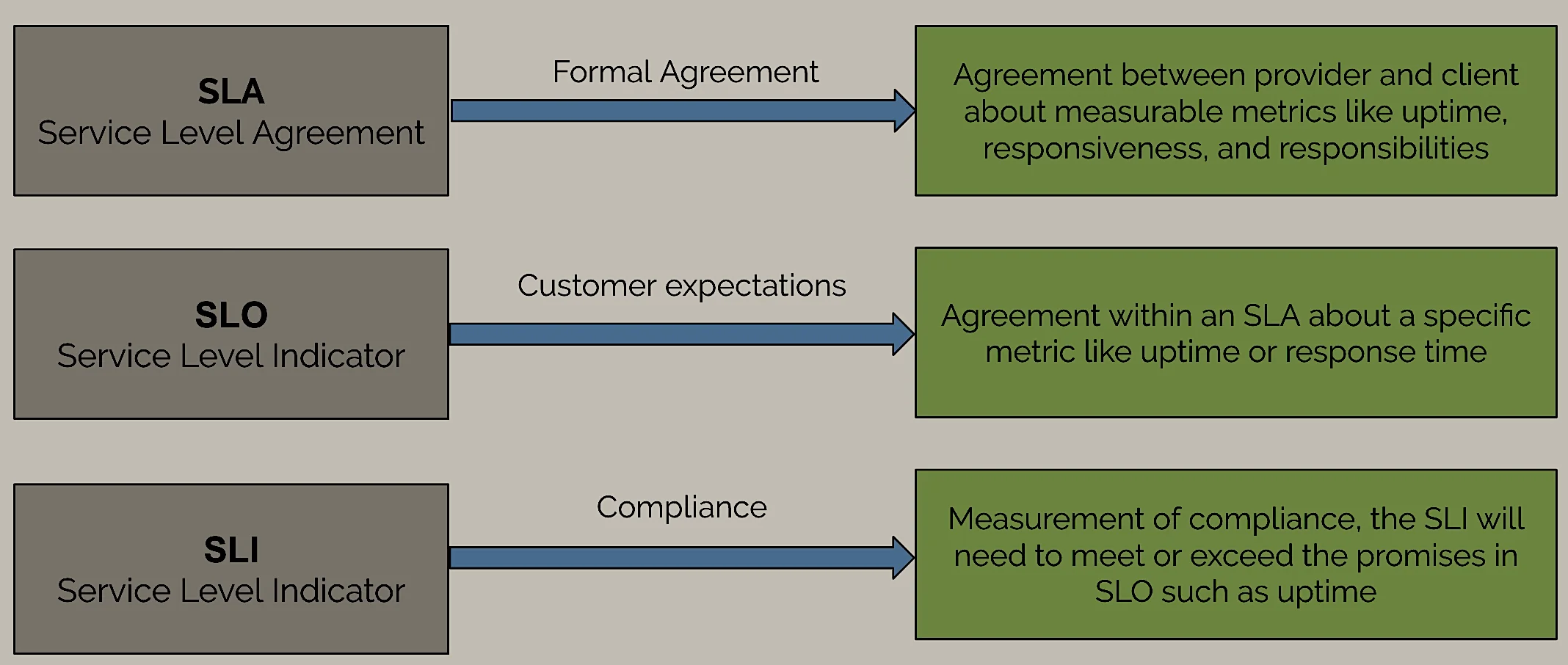
GitOps 3 initialisms
ArgoCD in 5 mins (Example)
PreRequisites
To be installed and running
Set Alias
alias k=kubectlCreate namespace and install argocd in your local cluster
- k create namespace argocd
- git clone https://github.com/marcel-dempers/docker-development-youtube-series.git
- cd docker-development-youtube-series/argo/
- k -n argocd apply -f argo-cd/install.yamlView running pods
k -n argocd get podsSet port forwarding
k port-forward svc/argocd-server -n argocd 8080:443Login to the UI
k get pods -n argocd -l app.kubernetes.io/name=argocd-server -o name | cut -d'/' -f 2
username: admin
password: (result of query)Deploy sample app and view in the UI
k apply -n argocd -f argo-cd/app.yamlDelete / Cleanup
- k -n argocd delete -f install.yaml
- k delete -n argocd -f app.yaml
- k delete namespace argocd